What Is OSINT in Cyber Security? A Complete Guide to Open-Source Intelligence
Open-Source Intelligence (OSINT) in cybersecurity involves gathering publicly available information to predict and defend against cyber threats. Hackers often use online data to target individuals, making OSINT a crucial defense strategy.

If there’s one thing the internet does well, it’s collecting and storing information—tons of it. It was built for that. At the beginning, it was a repository for data and communication—a military one at that. Then it went commercial. And once Facebook, Amazon, Apple, the CIA, and everyone else realized, these guys tell the net more things than they do at a therapist’s office—and it’s 24/7, that collection went into overdrive.
But what if I told you that a huge portion of cyber intelligence comes from publicly available sources? That’s right—no secret government databases, no hacking required. Just data hiding in plain sight. Don’t believe me? Google yourself—your SSN, your house, your address. It’s all there.
When hackers or scammers try to get their claws into you—and you wonder which organization sold your info—you’re thinking too big, too cinematic, too conspiracy theory. The most likely scenario? The hacker just went online, picked a random person, and started Googling them. Then, they rated that person as a potential target or not. How do they know you went to Tulum on vacation? Because you posted your photos and decided to review a restaurant in that region on TripAdvisor.
That’s the essence of OSINT in cyber security. Short for Open-Source Intelligence (OSINT), it’s the practice of gathering publicly accessible information and turning it into a strategic advantage—either to defend against threats or, at the very least, to stay ahead of the hacker.
So how does OSINT in cyber security actually work, and why does it matter? Let’s break it down.
Who Watches the Watchmen?
Security teams, ethical hackers, and even government agencies use OSINT cyber security tools to:
Track emerging threats before they escalate.
Analyze cybercriminal behavior on dark web forums.
Identify vulnerabilities before attackers do.
Monitor leaked credentials and data breaches.
But let’s be clear—OSINT is a double-edged sword. While security professionals use it for defense, hackers also use OSINT to craft convincing phishing campaigns, steal credentials, and launch targeted attacks.
What your team is using to protect you—even to give you an edge—is also what the hackers are using to get their claws into you.
“Well,” you ask, “isn’t there a way to not have that data floating out there?”
Sure, you can strip some of it—though not all of it—from the grid. All you have to do is stop posting, stop interacting, stop being active on the web. Think you can do it?
What Is OSINT in Cyber Security
Every day, 2.5 quintillion bytes of data are created online. That’s a mind-boggling amount of information, much of which is freely available—if you know where to look. It’s there, free for the taking.
Unlike classified intelligence, OSINT gathers data from publicly accessible sources, including:
Social media and public forums.
Government records and databases.
News articles and blog posts.
Leaked credentials and dark web markets.
The trick isn’t finding the data—that’s easy—but making sense of it. Getting through all the noise and pinpointing where the melody is—filtering, analyzing, and extracting insights that matter. That’s what OSINT does.
Why OSINT Is Critical for Cyber Security
Hackers are masters of reconnaissance—gathering intel on targets before launching attacks. A skilled hacker—one who really wants a target and has that target in sight—does a full profile on that target and finds out where they are bleeding. And they don’t need fancy cinematic hacking skills to do it. A quick Google search, some LinkedIn stalking, and a peek into breached data can reveal:
Employee email addresses for phishing scams.
Exposed company infrastructure (like unsecured databases).
Passwords leaked from past breaches.
Now flip the script. Security teams use OSINT for cyber security to:
Detect cyber threats in their early stages.
Identify leaked credentials before they’re exploited.
Monitor hacker forums and dark web activity.
It’s a game of who sees it first—security teams or attackers. It’s not about erasing that data—although some can be removed—but about finding it before the other guy does and using it, or at the very least incorporating it into your defenses.
Key Sources of OSINT in Cyber Security
Some intelligence comes from legitimate sources, while others require digging into the dark corners of the web — and each one requires a different take on OSINT.
Public Websites and Social Media
People overshare online—big time. It’s not just how ate what and that funny cat video — it’s data that can be used. Information that can be exploited. Think about your Instagram feed — all the things you share there. Photos of your kids, pictures of your gym, what clothes you like, where you live, what you do for a living. Attackers scour public posts to gather intel on companies and individuals. Security teams monitor:
LinkedIn and company websites for leaked internal information.
Twitter and forums where hackers discuss exploits.
Pastebin and breached data dumps for compromised credentials.
Government Databases and Public Records
Governments store vast amounts of data, much of which is open to the public. Security analysts scan:
Business registries and tax filings for organizational insights.
Patent databases to uncover new technologies targeted by cyber espionage.
Dark Web and Deep Web Intelligence
The dark web is where cybercriminals operate away from Google’s reach. OSINT tools track:
Stolen credentials for sale on hacker marketplaces.
Leaked corporate data from ransomware groups.
Conversations about zero-day exploits before they go mainstream.
The Role of OSINT in Cyber Security Operations
Threat Intelligence and Risk Assessment
Security teams use OSINT to predict and work against threats before they become breaches. This includes:
Monitoring hacker forums for leaked vulnerabilities.
Tracking malware trends to strengthen defenses.
Identifying new phishing domains before they are weaponized.
OSINT for Ethical Hacking and Penetration Testing
Ethical hackers use OSINT to simulate real-world cyberattacks by:
Gathering intelligence on a target (email addresses, subdomains, IP addresses).
Identifying weak security practices (like exposed admin panels).
Using publicly available data to bypass authentication methods.
Ethical hackers? Yes, those are called white hats. Basically, they go at you under the idea of what a black hat hacker would do. Think of it like playing Devil’s Advocate. These hackers are essential for security teams. Why? Because they think and act - to a degree - like the enemy. It’s sort of like having a domesticated Hannibal Lecter on the team.
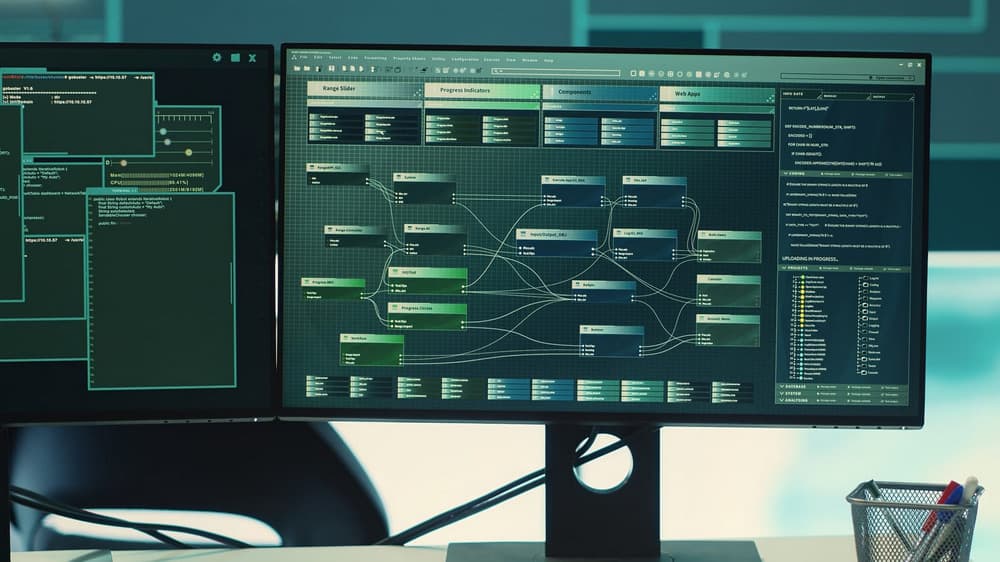
OSINT Cyber Security Tools & Techniques
Top OSINT Tools for Cyber Security
There’s an OSINT tool for everything—from tracking social media posts to scanning the dark web.
Maltego – Visualizes relationships between people, organizations, and data points.
Shodan – Scans the internet for exposed IoT devices, servers, and open ports.
SpiderFoot – Automates OSINT gathering from multiple sources.
Twint – Extracts intelligence from Twitter without an API.
DarkSearch.io – Indexes the dark web for security research.
OSINT Methodologies: Passive vs. Active Gathering
Passive OSINT – Collecting publicly available data without interacting with a target (For example, scraping LinkedIn for employee names).
Active OSINT – Engaging directly with a target’s infrastructure (For example, testing for misconfigured databases).
OSINT in Social Engineering & Phishing Attacks
Hackers love OSINT because it helps them customize their attacks. A little LinkedIn research and boom, they have:
An executive’s work email and travel schedule (for spear-phishing attacks).
Employee social media activity (to impersonate co-workers).
Internal company details to make phishing emails look more legitimate.
LinkedIn is a hacker's fantasy come to life — why? Because you need it. Today, most professionals require an active presence on that platform. And not only a presence but the key operational word in that sentence is “active.” What does this mean? It means they need to share and over-share about their work life.
The Future of OSINT in Cyber Security
With data breaches at an all-time high, organizations can’t afford to ignore OSINT. The future of OSINT in cyber security will include:
AI-driven OSINT automation to process massive amounts of data.
Stronger dark web monitoring to track cybercriminal activity.
Better OSINT training for security professionals to close intelligence gaps.
OSINT: A Game-Changer in Cyber Security
It’s an odd world, the one we live in — it’s a world where that old saying “can’t live with it can’t live without it” has gained much more prominence.
Tech is going nuclear — and not just because of its power but because it’s become so fast. Nuclear because, like the bomb, in a second, it can restructure a whole civilization.
And, like the bomb, the genie is out of the lamp. Nuclear power is vital for our survival, while at the same time being akin to playing Russian Roulette. AI is here to make new roads and headway, while at the same time, it’s here to close down shops and put people on the street. And that same tech is being employed by white hats to protect you, and black hats to hurt you.
And that’s just one of the many, many icebergs that are showing just the tip.